The Next Billion-Dollar Security Stack
The silent change in cybersecurity value-chain is set to create the biggest investment opportunity in enterprise & public infra
The one word that comes to my mind when I think about cybersecurity is transformation. there is a stark contrast between U.S.-based companies and their Indian counterparts. While U.S. firms are advancing rapidly, launching products to optimize the costs, expand value and defend against AI driven threats, the listed Indian universe remains dominated by service players.
The real hidden value lies in the startup ecosystem, where companies are silently replacing legacy solutions with new-age platforms that are at par with, if not superior to, their Western rivals. This shift is critical: in an increasingly volatile geopolitical climate, self-sustainability is paramount. Building internationally competitive, product-oriented companies is the need of the hour, and we are not far behind.
To understand why this shift is so significant, we have to look past the existing understanding of the cybersecurity value-chain.
For over a decade, the industry has been built on a fragmented model.
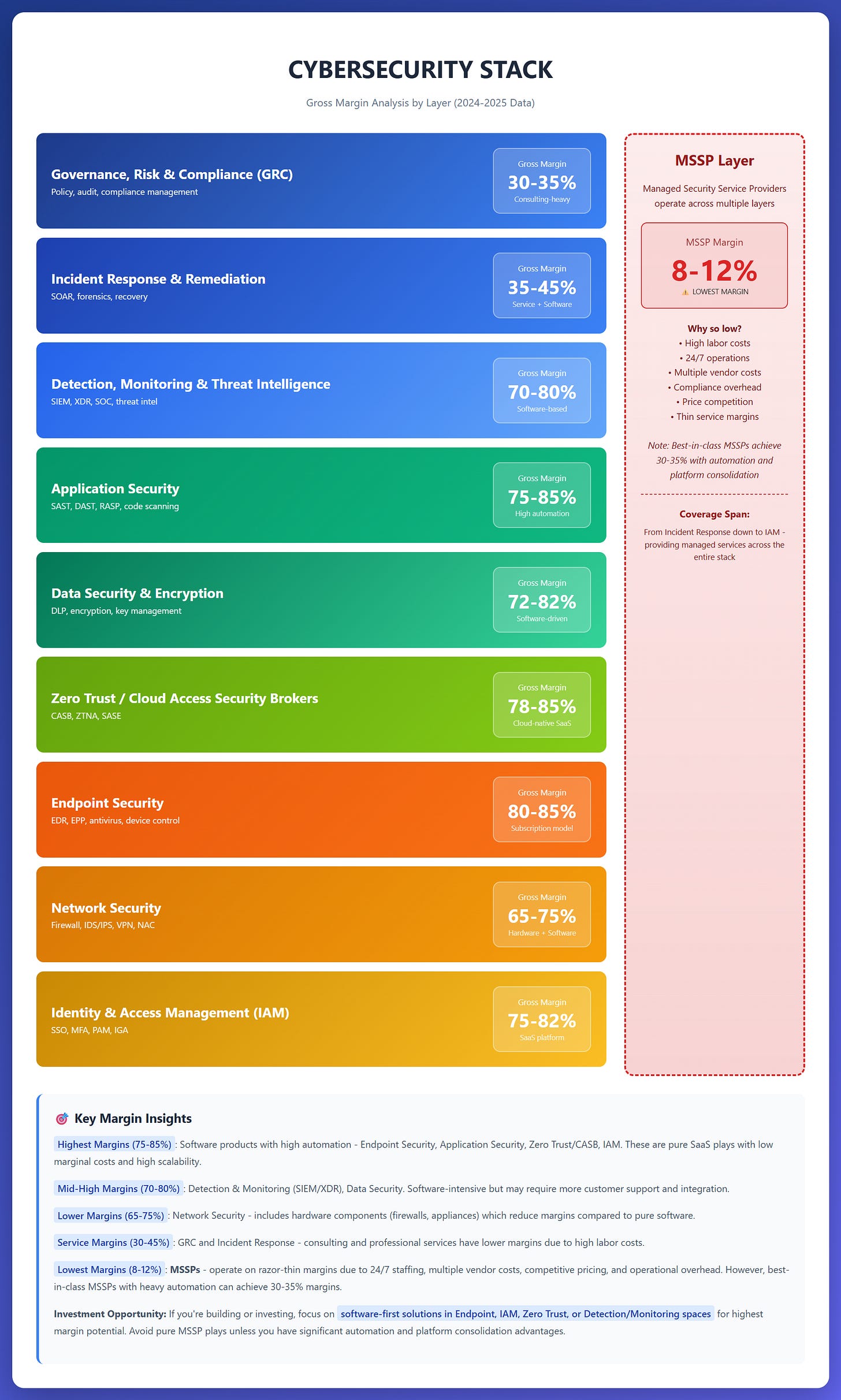
Take a look at cybersecurity stack with margins of each sub-segment within. This will be helpful when you study companies.
What we have in India-Listed universe is one company in the top layer, some in the Endpoint Security and the rest is all MSSPs - Managed Security Service Providers. Thinks of MSS as SIs for global security OEMs.
The new value-chain
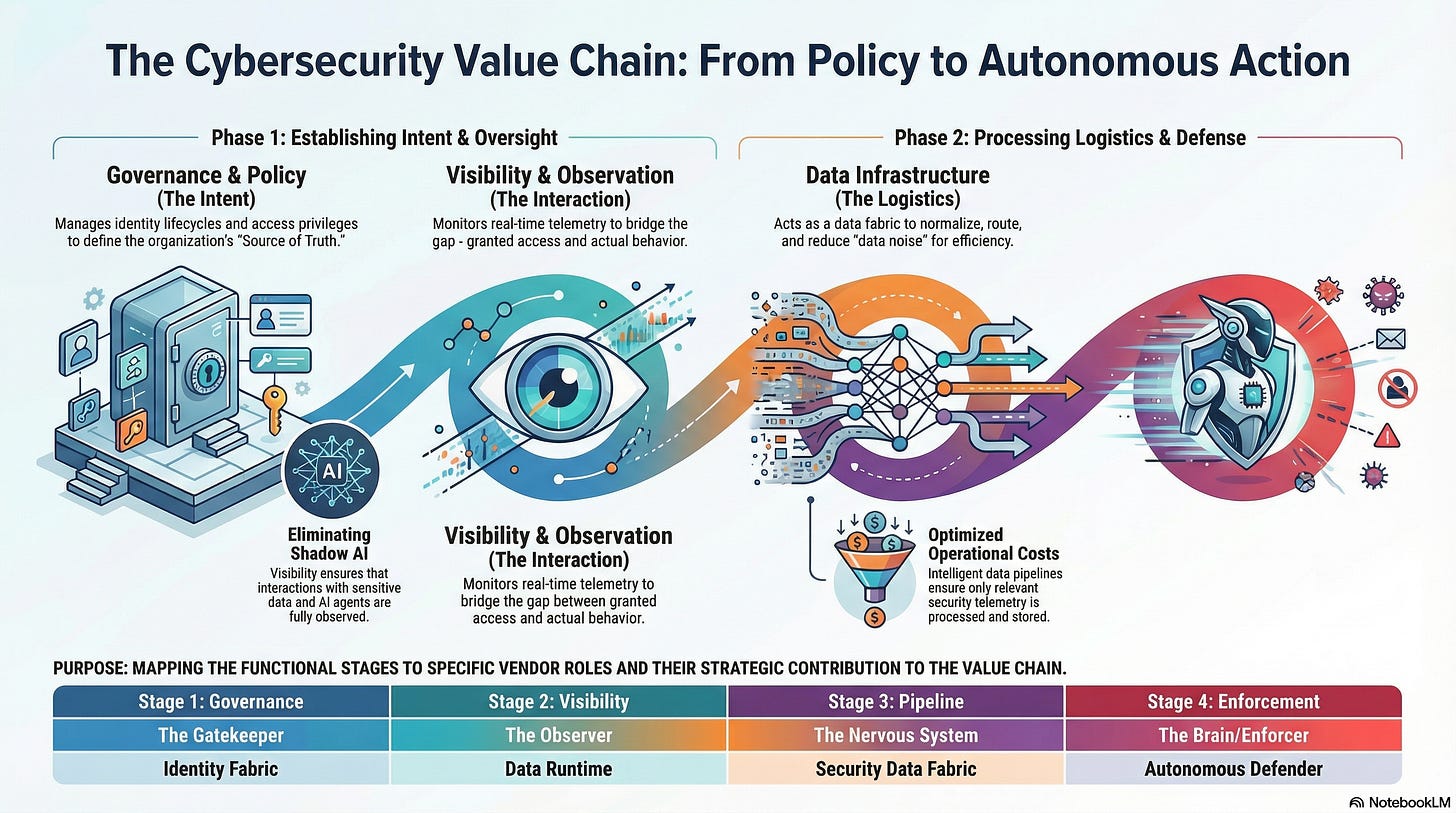
The first image shows you how today’s stack is and how is it transforming.
1. Governance: Establishing the “Source of Truth” and intent.
2. Visibility: Real-time observation of interaction vs. policy.
3. Pipeline: The logistical stage where data generated from previous two stages is optimized.
4. Enforcement: The “Brain” executing machine-speed autonomous response.
Everything starts with intent. In the cyber world, this is Stage 1: Governance. If you don't have a definitive record of who should be in your system, the rest of your security stack is just guessing. Historically, this was a mess of disconnected spreadsheets and legacy software.
With corporates slowly realizing the importance of managing an Identity, companies are moving beyond the basic login. They are converging identity management with privileged access, essentially creating a unified "Gatekeeper" that audits itself in real-time. By dissolving the silos between different types of users such as human employees, remote contractors, and even AI agents. These platforms provide the foundational moat that every other layer relies upon.
The Interaction Layer
Visibility is where most enterprises fail. You can have the best gatekeeper in the world, but if you don’t know what people are doing once they are inside, you are flying blind. This is especially true in the new agentic era, where AI agents are querying databases at a speed no human can track.
Companies are keen to monitor at the deepest kernel level without slowing down the system. Startups that provide a deeper view into data flows are need of the hour. These startups don’t just see that a user has accessed a database but they see that an unauthorized AI bot tried to scrape a million rows of information. It bridges the gap between the stated rules and actual behavior.
The Logistics: Solving the data drag
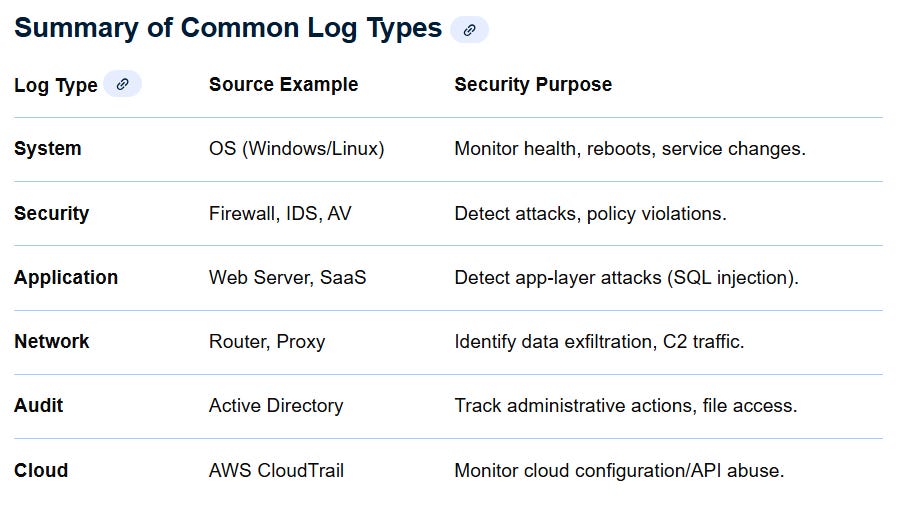
First, let us understand where does data generate from. Within an enterprise, data can be generate from a number of sources:
When you have so many sources constantly spewing out data logs, the systems that ingest these logs for remediation get overwhelmed.
One of the biggest hurdles in security is the sheer cost of data. Legacy providers have essentially strapped the growth by rooting for more data, charging more as companies generate more security logs. This is Stage 3: The Pipeline.
And, this is a very high margin space. The companies that manage & optimize data pipeline through normalization & filtering at source help reduce this burden significantly.
By stripping out the noise before it hits the expensive storage layers, they transform “Big Data” from a cost-liability into “High-Fidelity Data.” This logistics layer is the unsung hero that makes AI-driven defense actually affordable for a large-scale enterprise or a government department.
The Enforcement: Autonomous Response at Machine Speed
Finally, we reach the “Brain.” In a world where an attack can cripple a power grid in seconds, waiting for a human analyst to click “Approve” is a recipe for disaster. We are moving toward Autonomous Enforcement.
Autonomous Platforms represent the pinnacle of this value chain. Their “Agentic AI” doesn’t just send an alert to a dashboard but it investigates the threat and kills the malicious session instantly. This creates a “Self-Healing” loop: Stage 4 (Action) feeds back into Stage 1 (Policy), updating the rules, guidelines based on threat & remediation.
If you wish to see how I envision this, check this infographic that I generated with NotebookLM. This is distilled view into what we have just discussed. And, there is a startup for each of the 4 segments that I track for my personal academic interests. Perhaps, when the time is right I will mention their names but my intent of writing this post is to show you that India’s security stack is changing silently. Take this post as an input to your sectoral research or as a directive that will guide you in identifying companies for future investments.
Conclusion: Cybersecurity as a Pillar of Sovereign Power
Geopolitics is playing key role in government’s key policy decisions. We are living in an increasingly fractured world and every nation, every government wants to protect digital sovereignty. Every nation wants to protect its data, banking systems, power grids and so much more without external dependencies.
For years, India has relied on Western security players to protect the critical infrastructure. And, that has become a strategic risk to our digital sovereignty. Just as the U.S. leverages its native players to secure its assets, India must cultivate an internationally competitive, product-oriented ecosystem.
And, India is building. We have some amazing startups, completely home growth, designed to take over from Western counterparts without compromising on quality. Based on the interactions I have had with the founders, I believe we aren’t just building software, we are building the self-sustaining foundation for our digital infrastructure.
I truly believe that we are no longer lagging behind; we are ready to lead.


Love your writing Ameya bhai. Pls do it more often
Thanks for the long one bhai could get some sense into it.